Almost all of us, administrators of SBS servers, did a migration from one version to another several times. But in this moment we have at least two problems: SBS doesn’t exist anymore (and we have to do a hybrid deployment) and the new situation – the Essentials server 2012R2 doesn’t have a migration mode. So, I decided to write a blog how to migrate the SBS 2003 AD to the Essentials Server 2012R2 step by step.
Maybe in this steps there is a restart that is not really necessary, but please, do it. This is the only way that grants you success to migrate the AD and finally install the Essentials role successfully. Take your time and go through this steps:
- Start with uninstalling or disabling features of the SBS 2003. The first thing to do is to uninstall the ISA server (if it is installed – not covered in this article) and run the Connect to internet wizard again.
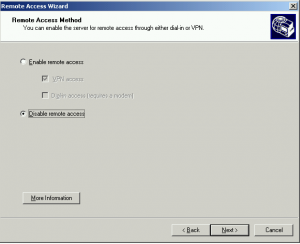
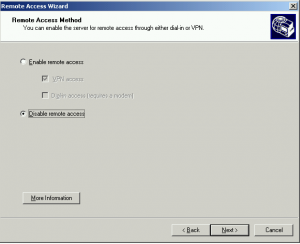
- Restart the SBS Server. If you have enabled the VPN, run the Configure Remote Access Wizard and disable the VPN access. Don’t forget it! You will not be able to disable it later!
- Shutdown the SBS Server and remove the second NIC (the NIC that is connected to Internet).
- Add the router to the network and configure the port redirection (for now to the SBS server – you need this step because you must receive E-Mails, grant remote access,…Do not forget to forward ports 80, 443, 25 and 987 – not covered in this article).
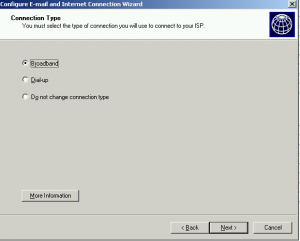
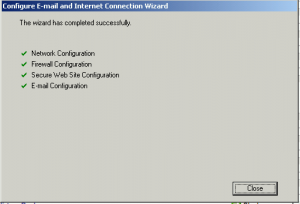
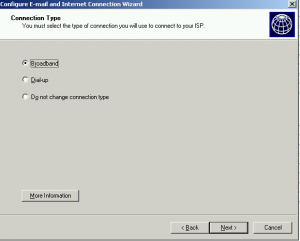
- Start the SBS Server and run the Connect to Internet Wizard again:
- Select the Broadband connection.
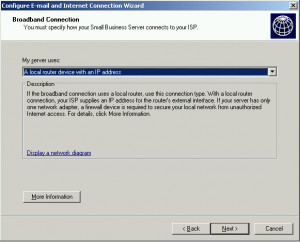
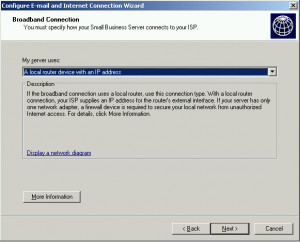
- From the dropdown menu select I have a router device with an IP address.
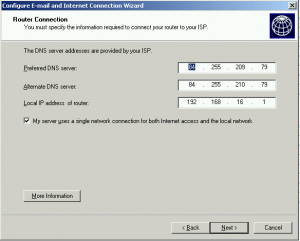
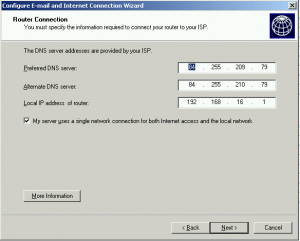
- Add DNS names from your ISP and the gateway address (the IP of the router).
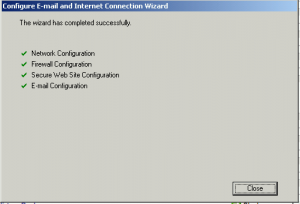
- Finish the wizard with defaults settings.
- From C:\Windows\Sysvol\Sysvol\DomainName\scripts delete the SBS_LOGIN_SCRIPT.bat file. This file is present in any SBS user as logon script and you have to delete it from all of the users as well.
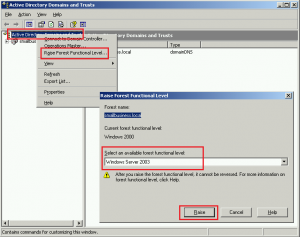
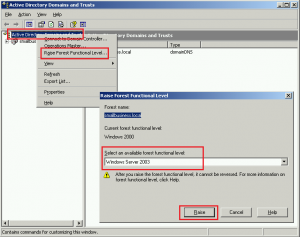
- Form the Start Menu > Administrative tools, start the Active Directory Domains and Trusts. In the left panel, right click on Active Directory Domains and Trusts and select Raise Forest Functional Level. Raise the forest level to the Windows Server 2003 version.
- Restart the SBS Server.
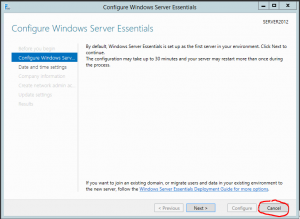
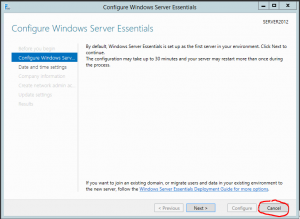
- On the Essentials server, on the Configure Windows Server Essentials wizard, press Cancel.
- Open the Control Panel > System and Security > System and change Computer name. Leave the compute member of workgroup. Be careful: you have to rename the computer in this step, you cannot rename it after the Configure Windows Server Essentials wizard is finished.

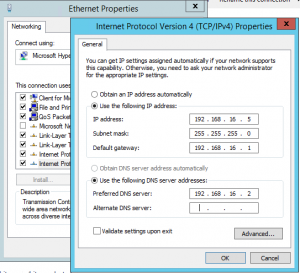
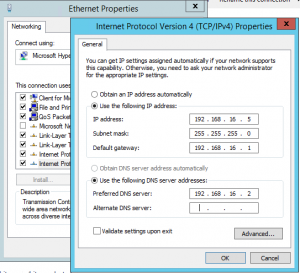
- My suggestion: From Start > Run type ncpa.cpl, right click on the network connection. Select properties and configure the static IPv4 address. As a DNS server, add a SBS Server IP address.
- Restart the Essentials Server.
- Open the Server Manager (not Dashboard!) and select Add roles and features. In the Add Roles and Features Wizard, install the Active Directory Domain Services role.
- Restart the Essentials server.
- On the Configure Windows Server Essentials wizard, press Cancel again and start the Server Manager again.
- From Server Manager > Notifications (up right corner) run Promote this server to a domain controller task.
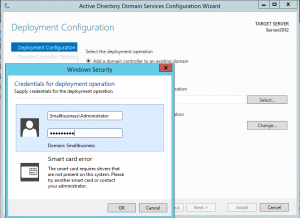
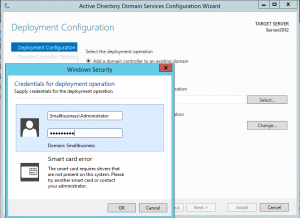
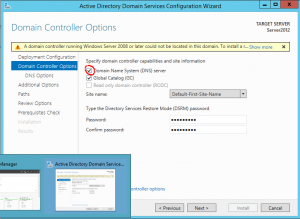
- When the wizard is open, on the first page select Add a domain controller to an existing domain and enter the SBS admin credentials. When you will confirm this credentials, the Domain field will fill automatically. Click Next.
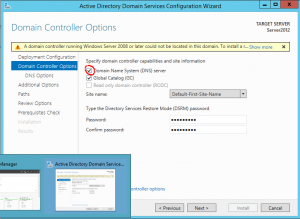
- The next step is to enter the DSRM password (complex, 8 or more characters) and be careful to check the checkbox of the DNS server! Click Next.
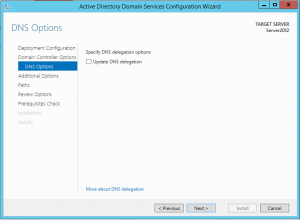
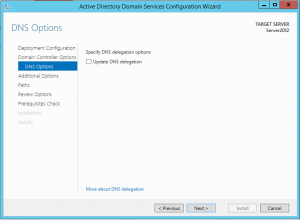
- Clear the checkbox on Update DNS delegation and click Next.
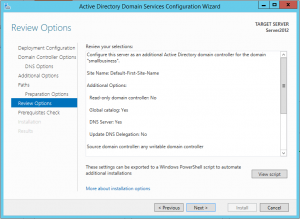
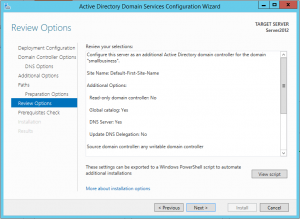
- In the next few steps click Next. In the Review Options check that all options are OK and click Next once again.
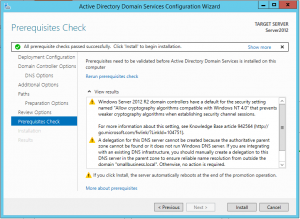
- In the Prerequisites Check step, you will receive some warnings. This is nothing serious and you are ready to promote this server as an additional DC in the SBS domain. Click Install.
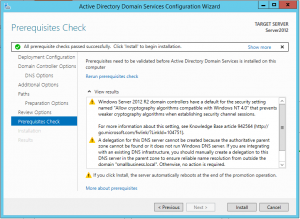
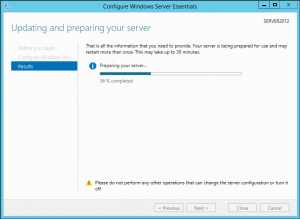
- During the installation, the domain schema and the forest schema will be automatically upgraded. The process could take a while. After the installation is finished, the server will restart.
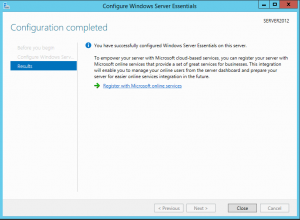
- Logon to the server with the SBS administrator domain credentials.
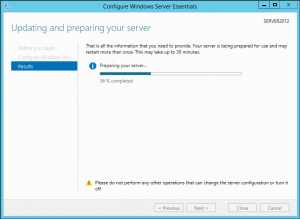
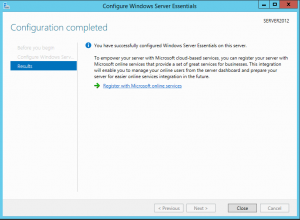
- Complete the Configure Windows Server Essentials wizard.
- My suggestion: Install the DHCP server on the Essentials Server. Do not use the router as DHCP server. Check forwarders in the DNS server. You have to use only the ISP DNS servers as forwarders or, if you prefer, you could not use any forwarder.
At this point, the Essentials Server 2012R2 is added as an additional DC in the SBS domain. Be careful, because you have only 21 days to complete the migration and you still have a lot of work. You have to transfer all the shared folders data, the Exchange mailboxes, the SharePoint data,… Please do not forget to control and change some settings on the GPO. Remove some GPO (some are set strictly for the SBS).
Be aware, that all workstations have to be added to the “new” domain once again true the connect site.
Be careful also when you will turn off your old server. You cannot just turn it off. You have to uninstall at least the Exchange and the DC role, but I prefer to uninstall all the installed roles, remove the server from the domain (make it part of a workgroup) and after this I turn it off.
Please let me know if you want me to write additional blog posts on migrating other functionalities of SBS..