As system administrator I always prefer to be the first one who upgrades to new versions (if there are some bugs, I know them in advance). Of course, also in this update, there are some bugs…
In my upgrade, I found these problems:
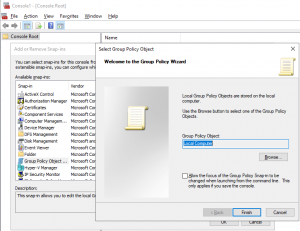
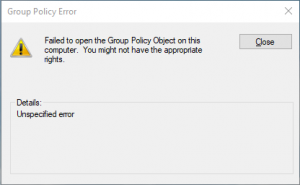
- Unable to edit Local Computer Policy: – this is not difficult to solve and will take just a second and a computer restart:
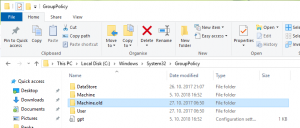
- Open Windows Explorer and go to the folder C:\Windows\System32\GroupPolicy (it is hiden; you have to type it)
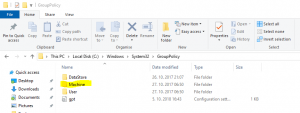
- There you will find a folder Machine. Rename it to something else (Machine.old for example)
- Try to open Local Computer Policy again
- Restart the computer just to be sure that all policies are applied.
- Open Windows Explorer and go to the folder C:\Windows\System32\GroupPolicy (it is hiden; you have to type it)
- Microsoft Edge is not able to connect to almost any page (Cannot securely connect to this page). Here it can be more complicated and you should try more things. Let’s start in the right order:
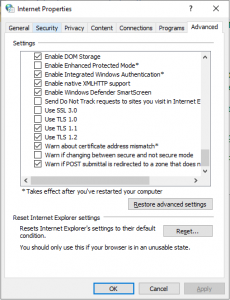
- Review if TLS 1.1 and TLS 1.2 are enabled:
- Antivirus. Can be a course of the issue. Try to disable or better uninstall antivirus services (disabling is not always enough). Look also on the knowledge base of antivirus company. It was my case. If you have Sophos, here is an article about this issue.
- Check the network drivers and update them to the latest version (yes, in some cases this can be a source for the issue; Edge depends on this drivers)
- Disable, than reenable IPv6 and after this execute also ipconfig /renew.
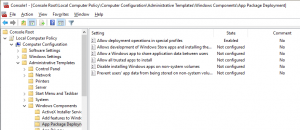
- Change the setting in Local Computer Policy.
- Reinstall Microsoft Edge:
- Open PowerShell as Administrator
- Run the following cmdlet: Get-AppXPackage -AllUsers | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register ‘$($_.InstallLocation)\AppXManifest.xml’
- You may receive some errors during the installation, but don’t care about them.
- If nothing of this will works, Microsoft recommends reinstalling Windows.
Hope that I helped someone on time. Tomorrow will be a patching date.